Iranian hackers’ cyberattack on US: 5 times modern warfare went online

When Stryker employees showed up to work one morning in March 2026, their laptops were bricks. Their phones had been wiped. Across 79 countries, 200,000 devices bore the same image: the logo of Handala, an Iran-linked group settling a score for a US Tomahawk missile strike that killed 175 people, most of them children, at an Iranian school. They hadn’t planted malware. They’d logged into Stryker’s own Microsoft Intune console and hit factory reset on the entire company. Welcome to the new shape of war.
 Survey
SurveyAlso read: Iran-linked hackers claim cyberattack on medical giant Stryker, disrupt global systems
India-Pakistan’s digital war game (2025)
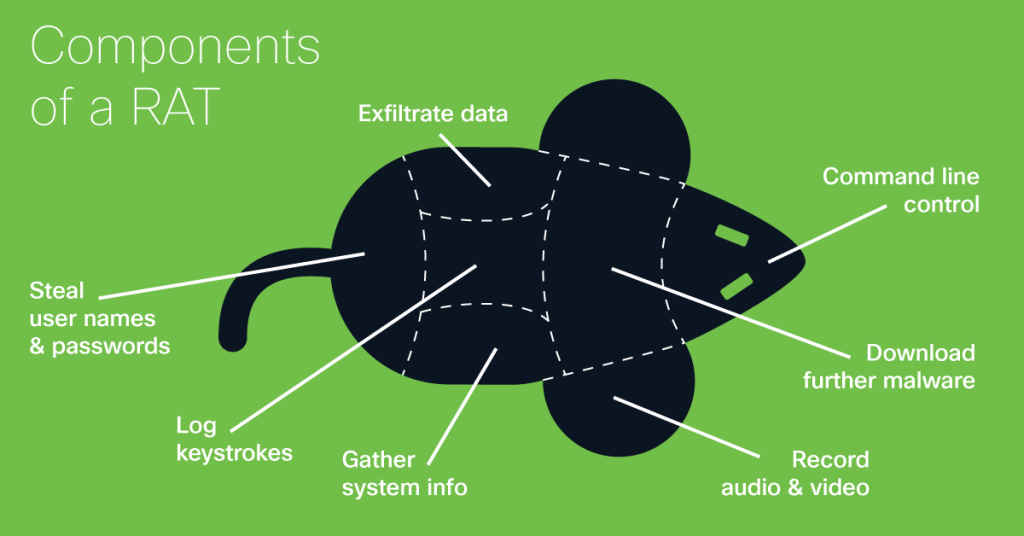
When Indian forces launched Operation Sindoor in 2025, Pakistan didn’t just respond on the ground. APT36, a Pakistan-linked hacking group, ran a parallel digital offensive, spear-phishing documents disguised as official briefings, including one named Preventive_Measures_Sindoor.ppam, dropped Remote Access Trojans across Indian defense networks. Boots on the ground, malware in the inbox. The two operations ran simultaneously.
Russia’s war on paperwork (2024)
In December 2024, Russian-linked XakNet disabled 14 Ukrainian state registries in a single operation. Border guards couldn’t verify travel restrictions. Notaries were blocked from completing transactions. Real estate records vanished. No missiles were required, just administrative paralysis, which has become as deliberate a Russian war objective as taking territory.
Also read: Elon Musk’s Starlink shaping 2026 Iran-US-Israel cyber war, here’s how
Sting & Zerlot (2025)
Early 2025 brought a grimmer escalation. Russian group Sandworm deployed two wipers simultaneously, Sting for Windows systems and Zerlot for Linux, against Ukrainian universities and energy facilities. The cross-OS approach was deliberate: hit both environments at once and leave no recovery path. Data destruction as a military tactic, refined to the point of elegance.
The Arsonist breach (2024)
Following the escalation in Southern Lebanon, Iran-linked Charming Kitten breached Israel’s Ministry of Defense and leaked 15GB of sensitive personnel data. The goal wasn’t disruption, it was fear. Expose the identities of active soldiers to their enemies and let the psychological damage compound on its own. No explosion required.
Aliquippa, Pennsylvania (2023)
Pro-Iran group Cyber Av3ngers hacked a water pumping station in Aliquippa, Pennsylvania by exploiting Israeli-made Unitronics PLC components. A local water authority became a casualty of a war being fought on another continent, because somewhere in its supply chain was a piece of Israeli hardware. The message landed clearly: the blast radius of modern conflict has no obvious edge.
All five attacks share the same logic as Stryker. They don’t steal. They stop things, services, institutions, trust. Building that kind of disruption used to require an army. Now it requires knowing where to look.
Also read: Intel India & Digital India BHASHINI partnership: Bringing multilingual AI to laptops
A journalist with a soft spot for tech, games, and things that go beep. While waiting for a delayed metro or rebooting his brain, you’ll find him solving Rubik’s Cubes, bingeing F1, or hunting for the next great snack. View Full Profile