Iran’s digital offensive: Cyber campaign will outlast physical one, says Tenable CSO

“The access obtained during these weeks, through compromised firewalls, pre-planted backdoors, exploited cameras and weaponized documents, will persist in Gulf and U.S. networks for months or years after the last missile is intercepted.”
 Survey
SurveyAlso read: Samsung Galaxy S26 Plus in Digit Test Labs: A flagship that sticks to its formula
That is the assessment of Robert Huber, Chief Security Officer at Tenable and it cuts to the heart of what makes Iran’s current offensive different from anything seen before. This is not simply a cyber campaign running alongside a kinetic one. The digital intrusions, backdoors and compromised devices being established right now are the foundations of a threat that will still be active long after any ceasefire is signed.
While drone strikes on Qatari LNG terminals and the physical destruction of two AWS data centers in the UAE have dominated the headlines, Huber argues that the more consequential battle is playing out somewhere most organizations aren’t watching closely enough.
Also read: Who is Jasjeet Sekhon: CSO of DeepMind, AI career, causal inference expert
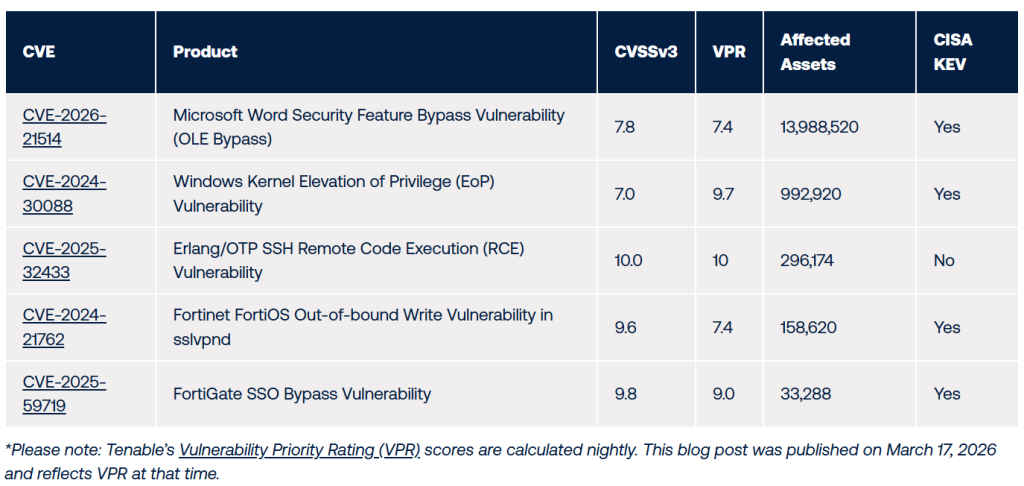
Tenable’s Research Special Operations Team analyzed asset exposure data across the seven countries in Iran’s crosshairs and found over 15.5 million affected assets. The main finding is a single Microsoft Word vulnerability – CVE-2026-21514, an N-day that bypasses security prompts without alerting users – accounts for nearly 14 million of them. It was added to CISA’s Known Exploited Vulnerabilities catalog in February and has functional exploit code in the wild.
The geographic breakdown adds another dimension. Despite the Gulf states facing the most acute conflict-specific targeting, the United States accounts for 15.4 million of those 15.5 million affected assets, 99.4% of the total. Healthcare and government are the most exposed sectors, with 1.75 million and 1.1 million affected assets respectively, both verticals explicitly in Iranian actors’ sights.
For Huber, the numbers reveal a critical flaw in how organizations are currently responding. Threat intelligence naturally gravitates toward the most visible and novel threats, in this case, the exploitation of IP cameras for missile targeting and the Handala wiper attack on medical technology firm Stryker, which wiped nearly 80,000 devices across 79 countries. Both are serious but neither of them tells the full story.
There is also a very small window to act. Iran’s internet connectivity is currently running at just about 1 to 4%, hindering the abilities of state sponsored groups like MuddyWater and OilRig to coordinate sophisticated operations at scale. When that changes, pre-positioned backdoors already planted inside critical infrastructure become activatable. The missiles may eventually stop but the cyber campaign, as Huber warns, will not.
Also read: Asus TUF gaming laptops of 2026 announced: 5 things to know
A journalist with a soft spot for tech, games, and things that go beep. While waiting for a delayed metro or rebooting his brain, you’ll find him solving Rubik’s Cubes, bingeing F1, or hunting for the next great snack. View Full Profile