Telegram Messenger plugs loophole that leaked users’ IP addresses during calls
The bug was found by security researcher Dhiraj Mishra in Telegram for Desktop and has been fixed in 1.3.17 beta and 1.4.0 versions.

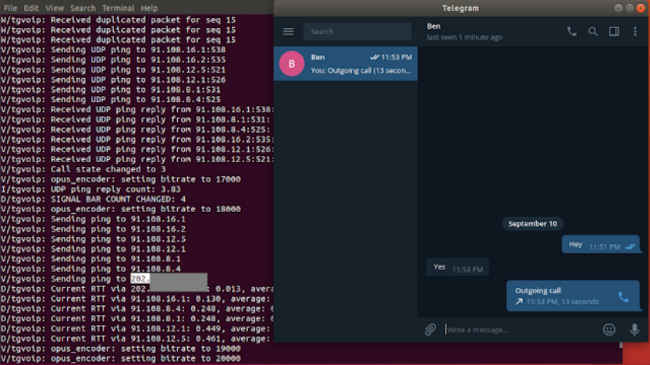
Telegram has fixed a bug that was leaking IP addresses of users who were placing calls using the Telegram for Desktop app. The bug was found by security researcher Dhiraj Mishra who said that a default setting led the app leak the above-mentioned information during voice calls. As per Bleeping Computer, when using Peer-to-Peer (P2P) to initiate Telegram calls, IP address of the receiver will appear in the Telegram console logs.
 Survey
SurveyTelegram Messenger is a communication app that allows users to use encrypted chats and phone calls over the Internet. Under the settings menu (Settings –> Private and Security –> Voice Calls –> Peer-To-Peer) you can see that the app gives users an option to prevent their IP address from being revealed by changing the default setting “Always” to “Never”. If a user does this, the calls will be routed through Telegram's servers, which would then hide the IP address but there will also be a drop in the audio quality. But this is only on iOS and Android. PCs powered by Linux or Ubuntu OS, the official Telegram for Desktop and Telegram Messenger for Windows applications did not offer the same ability.
Mishra illustrated how the IP address were leaked during the calls in a Proof of Concept video. After alerting Telegram about the loophole in Telegram for Desktop and Telegram Messenger for Windows applications, Dhiraj was awarded a bounty of €2,000 (approx Rs 1.70 lakh) and the issue has been fixed in the 1.3.17 beta and 1.4.0 versions of Telegram for Desktop, which bring the option of disabling P2P calls in the app.
Digit News Desk writes news stories across a range of topics. Getting you news updates on the latest in the world of tech. View Full Profile