Here’s how you can play your part in a cyber war
Everyone’s a soldier in the digital war
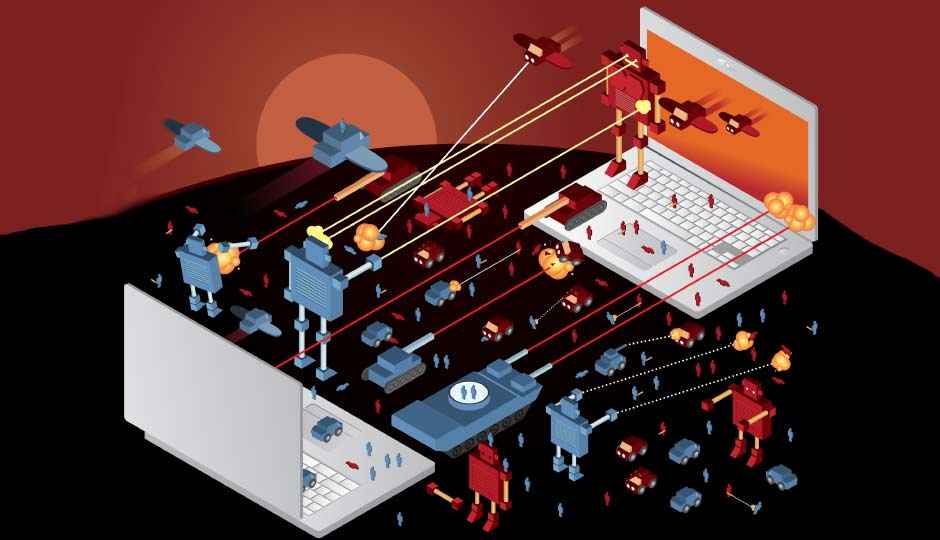
What is Cyber Warfare
Cyber Warfare is a theatre of war that has been in the news for quite a while but not clearly understood. While both forms of warfare are equally effective not much is known about cyber warfare. Cyber Warfare is simply the application of hacking methods to attack the opponent’s digital resources and thus, affect economical damage or extract intelligence. The average cyber soldier does not fit the image that comes to your mind when you hear the word soldier. And no, we don’t wish to imply that these are script kiddies based out of their parent’s basements either. Cyber warfare has been used effectively for quite some time and is being looked at as the primary means of extracting intelligence.
 Survey
SurveyMilitaries around the world have long fathomed the importance that cyber warfare has in the modern world and there have been quite a few publicly known operations as well. And not all of these operations were for military purposes. Some have been targeted towards civilian infrastructure, some acts of cyber warfare have been politically motivated acts of hacktivism, some have been in the private sector as a means of industrial espionage and lastly, certain acts were used as a means of gaining knowledge about the implications of cyber warfare (research, if you will). If you want a more recent example then by the time you are reading this, you’ll have been bombarded quite a bit about the set of DDoS attacks that have been happening since October 20th 2016. The sheer magnitude of this DDoS attack was such that large scale services like Spotify, Twitter, Github, PayPal and others were rendered inaccessible. At the time of writing this, not much has been revealed about the reasons for this attack nor had any entity come forward to own up.
What's our situation
What if we told you that we didn’t even have a cyber security policy in place before 2013? While the word hacking has been thrown around by folks for a better part of the decade, the Indian Government hadn’t given much thought to cyber warfare. It was only after the whole NSA blowout happened and Edward Snowden revealed that India had been spied upon for ages that the government woke up. Apparently, the NSA was focused on domestic Indian politics and commercial and strategic interests. After the revelation of 2013, the Department of Electronics and Information Technology came up with the National Cyber Security Policy to put up a framework in place.
It’s still an evolving framework and the Indian Computer Emergency Response Team (CERT-In) is one of the agencies to have been set up in the aftermath of the 2013 revelations. However, the more critical agencies like the Nuclear Power Corporation of India has chosen to build it’s own capabilities to deal with mission critical infrastructure while the CERT-In is given less critical sectors. Another body set up under the Department of Information Technology is the National Critical Information Infrastructure Protection Centre (NCIIPC). And under the watchful eyes of the National Security Agency, there’s yet another agency being set up about which not much has been revealed.
Doing your bit
For starters, let us put this little thing called a disclaimer right at the top. We don’t encourage you to go ahead and hack websites or send out DDoS attacks. These things are not so easy to execute for anyone without any prior experience and staying anonymous while doing so is also difficult. Additionally, if you are caught and prosecuted you’re guaranteed to either be incarcerated for a long time or at least be rendered bankrupt. The fines that such offenses carry are not small. Moreover, India has extradition treaties with roughly 48 countries and once the fog of war has risen and all is dandy between warring nations, you’ll be packed off and sent to a prison to serve a not so pleasant prison sentence. So yeah, anonymity is absolutely necessary should you go and get caught.
Where do you start?
So your country is at war and you’ve decided to do your part on the cyber frontlines. IRC chatrooms are often the first place you get started with. Quite a few of them will help you figure out how to be completely anonymous on the internet. Anonymous, the infamous hacktivist collective has their IRC chatroom publicly accessible on the internet at webchat.anonops.com. Join the #learninghub channel and get started with the concepts. Having knowledge about network topology and knowing at least one programming language (preferably C and C#) and a scripting language will go a long way towards making this a lot easier.
Setting up an OP(Operation)
If you are well versed with programming and want to commence an operation then you need to find a staging area. Pick an IRC network where you’re likely to find like minded Indians, and create an IRC channel for your OP. Ensure that you have a clear goal for your OP and build up a list of targets. For example, if you wish to target the electrical grid or the banking infrastructure of the enemy nation then find out which servers they run on and also whatever contingencies they have in place.
Put out a call to arms notice on your IRC general chatroom and get more people to join the cause. Once you have enough people on board, you need to break down your goal into smaller tasks that are to be assigned to smaller groups. Identify leaders for individual groups, maintain anonymity to the highest extent possible.
Your individual groups now need to figure out ways to disable the target be it through penetration or through a DDoS (Direct Denial of Service) attack. And you will have plenty of people signing up with no knowledge of hacking but still want to do their part. You can either create a DIY guide or build a bot using a builder kit like ZeuS. This is a well know builder kit so you’ll have to find your own or build one from scratch as most OPs do. The bot needs to have a settings configuration, an executable for the payload, a Command-and-Control host file for the bot to pull instructions from and lastly a backdoor which uses the Socket Secure protocol allowing you to remotely control the bot.
Once the bot is created, use any means necessary to propagate it. The wider it spreads the bigger your botnet becomes. And then you have to move on to setting up your Command and Control (CnC) server. Find any cheap service which doesn’t even check credentials and set up your CnC. Your CnC can be either static with a single server which becomes very easy to take down or you could create something akin to Stuxnet which would synchronise with servers in a random fashion to receive updates. Your bots will seek out this particular CnC for instructions.
You now have a botnet which should be growing rapidly waiting for instructions. The moment you believe you have enough bots live to take down the target infrastructure you may initiate a DDoS attack. There are multiple types of DDoS attacks and a well designed firewall can easily mitigate simple DDoS attacks. So a little creativity goes a long way towards making your attack a success. Individuals can also resort to using DoS tools like Nemesy, Blast and Panther to attack IP addresses but the popular tools are very easily countered and your IP gets logged quite easily. So stick to using a new tool, the newer a tool is, the more difficult it will be to counter the same.
If not hacking then what?
Be part of the propaganda machine! No seriously, if you find pro-Indian propaganda then go create a fake ID and use a VPN, then go to every nationalistic forum/Facebook page and plaster that propaganda. Even a few posts a day is enough. Your ID will get reported and possibly banned but you’ll be doing your part. Don’t be outright aggressive but act a little mature and you’ll be heard.
This article was first published in November 2016 issue of Digit magazine. To read Digit's articles first, subscribe here or download the Digit e-magazine app for Android and iOS. You could also buy Digit's previous issues here.
Mithun Mohandas is an Indian technology journalist with 14 years of experience covering consumer technology. He is currently employed at Digit in the capacity of a Managing Editor. Mithun has a background in Computer Engineering and was an active member of the IEEE during his college days. He has a penchant for digging deep into unravelling what makes a device tick. If there's a transistor in it, Mithun's probably going to rip it apart till he finds it. At Digit, he covers processors, graphics cards, storage media, displays and networking devices aside from anything developer related. As an avid PC gamer, he prefers RTS and FPS titles, and can be quite competitive in a race to the finish line. He only gets consoles for the exclusives. He can be seen playing Valorant, World of Tanks, HITMAN and the occasional Age of Empires or being the voice behind hundreds of Digit videos. View Full Profile


