Google removes 13 malware apps from Play Store that were installed over half million times: Report
These 13 apps are reported to have no functionality and would download another app in the background and prompt the user to install another app. This secondary app would display ads whenever the device was unlocked.

Seems like Google can’t catch a break when it comes to booting malware from its Play Store. The official source of Android apps recently removed 13 apps from its listings since they were malware disguised as apps. This comes after an ESET security Researcher Lukas Stefanko tweeted about these apps, demonstrating how they were fake and would hide their app icons on a device after being downloaded and installed. These apps would download another APK in the background called ‘Game Center’ and ask the user to install it. Once installed, this app too hides in the background and displays ads when the device is unlocked.
 Survey
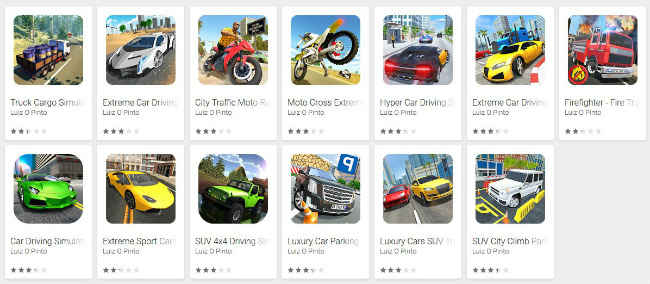
SurveyThese malware apps include a luxury car driving simulator, truck cargo simulator, fire truck simulator, among others. The thumbnail images of these apps were also well made and could easily be mistaken for legitimate apps. Stefanko said that these apps were cumulatively downloaded more than 560,000 times and all of them were made by the same developer named Luiz Pinto. He also shared a video demonstration of one of the apps. After installing and running it, the app crashes and hides its icon from the phone. All the thirteen malware apps didn’t have any functionality and two of them were said to be trending on the Play Store as well, before being pulled by Google.
In a similar case, researchers recently zeroed down on an app called “Couple Vow,” which allegedly exposed the login details of its 1.7 million users. Researchers said that they were able to request the data from the app’s server using “a GET request.” Using GET request means that there is no encryption in place to safeguard the sent data and the team found that there was no need of entering a username or password, all the user logins were unencrypted and anyone with an internet connection could read them. “You do not even have to attack the server. A single GET request gets you all the data as there was no authentication at all,” SIT Security Researcher Siegfried Rasthofer was quoted as saying. You can read more about this here.
App functionality demonstration pic.twitter.com/11HskeD56S
— Lukas Stefanko (@LukasStefanko) November 19, 2018
Digit News Desk writes news stories across a range of topics. Getting you news updates on the latest in the world of tech. View Full Profile