PlaceRaider Android malware spies through smartphone camera
The implications of PlaceRaider, a new experimental malware for the Android operating system, are frightening to say the least. Laying bare everything that you thought was private and secure within your Android smartphone and your surroundings, PlaceRaider takes inconspicuous photos from your smartphone to build a 3D model of your surroundings. PlaceRaider further gathers data and uploads it on a central server, letting hackers and robbers exploit you like never before.
 Survey
SurveyPlaceRaider is an experimental Android trojan developed by Indiana University and the U.S. Navy and it’s a new variant of malware under virtual threats that exploits a smartphone’s camera by capturing visuals. According to a report, PlaceRaider works on all versions of Android 2.3 Gingebread and above, disguising itself inside a photo app which gives it all the necessary access and permissions to take control of the infected smartphone’s camera. The trojan further takes photos tagged with the time, location and orientation of the phone, and the photos are taken quietly without the phone’s shutter sound.
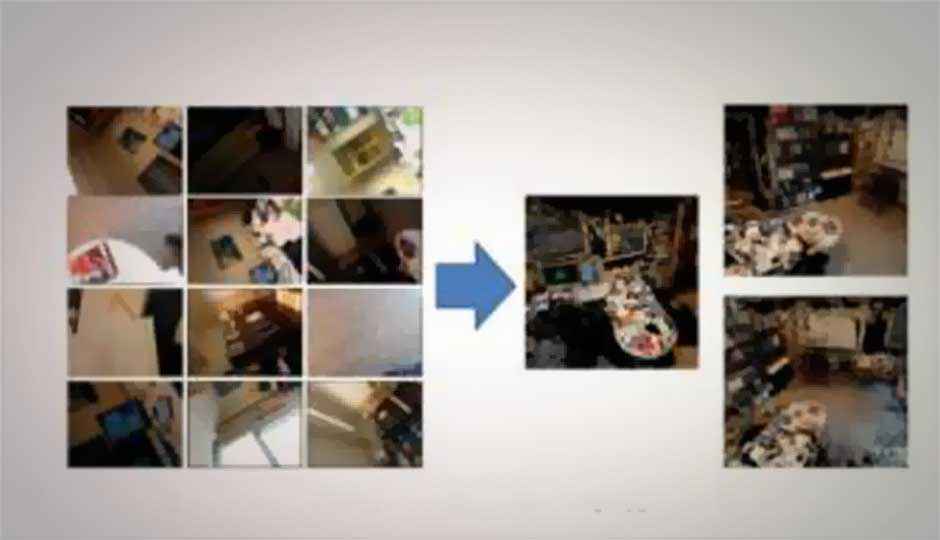
The troubling aspect of PlaceRaider’s experitise lies not only in its ability of taking photos of your surrounding through your Android smartphone, but it uploads the pics to a central server where they’re knitted together to a form a 3D representation of a person’s room or office layout. PlaceRaider’s software also boasts of the ability to identify the victim’s financial data — cheques lying around, credit card statements, bar codes, QR codes, etc.
Should you be worried about PlaceRaider finding its way into your Android smartphone and wreaking havoc with your private life? Not just yet. Since the trojan was created in a joint research project between the school of Informatics and Computing at Indiana University and the Naval Surface Warfare Center, chances of it reaching bad guys is slimmer than slim. Also the logistics involved in capturing images, knitting them together in a 3D model and analyzing them for a possible credit card statement… all this is very time and resource-intensive work. Wonder if many small-time hackers and malware delivery networks have such resources at their disposal.
For further information on PlaceRaider and how it operates, read the following research paper in full here.